The Economics of BEC: Why the Reported Loss Is a Floor, Not a Figure
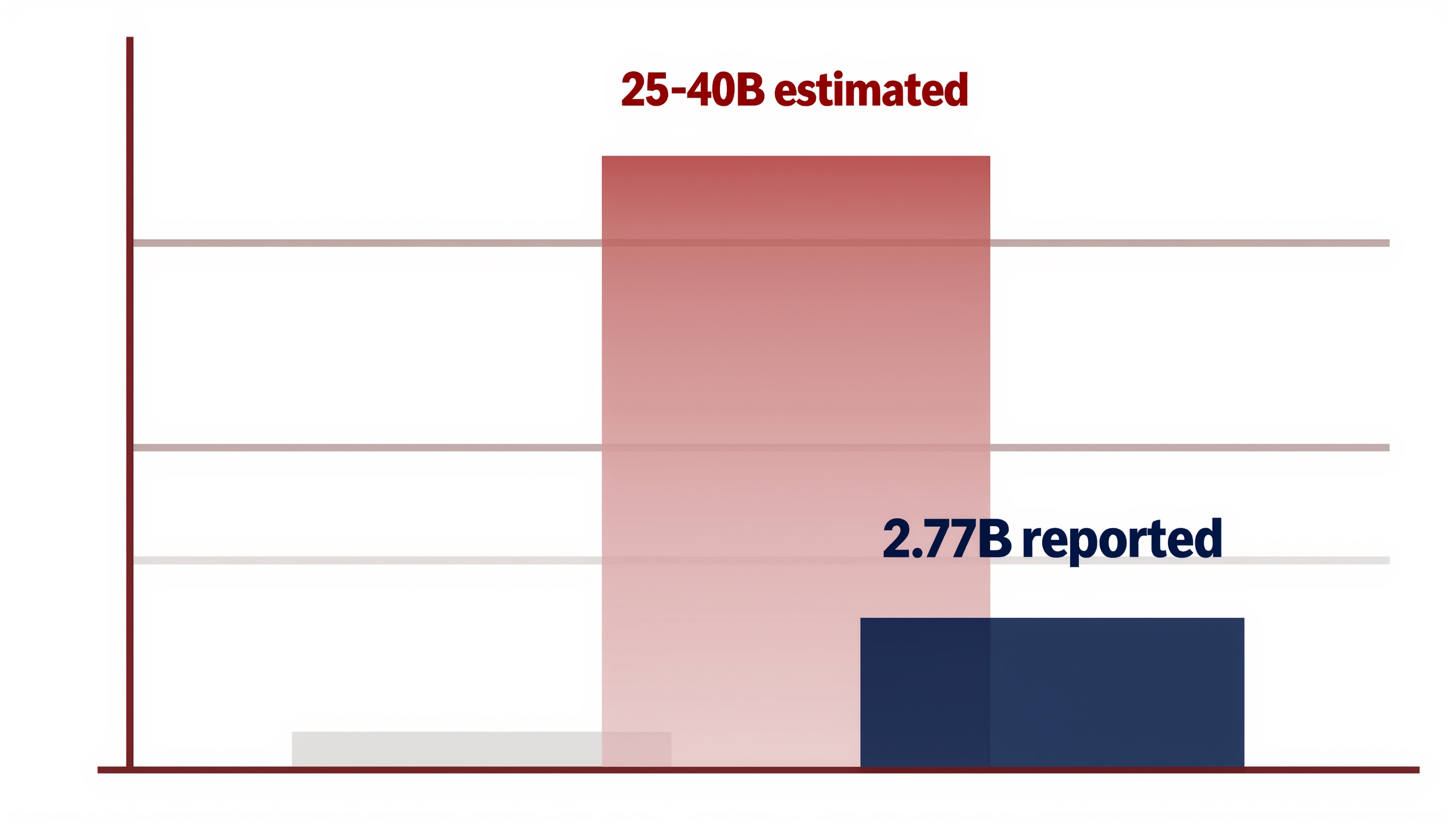
The FBI reported $2.77B in BEC losses for 2024. Three independent data flows suggest the real number is 10–15x higher. The arithmetic, and why it matters.
The FBI's Internet Crime Complaint Center published one of the most-cited fraud numbers in payments journalism last spring: $2.77 billion in Business Email Compromise losses across 21,442 complaints in 2024 1. That figure is quoted everywhere. Congressional testimony, bank security briefings, insurance underwriting models, CFO quarterly decks. It is treated as a measurement of the scale of BEC fraud in the United States.
It is not a measurement. It is the floor of a range, and the range's ceiling is somewhere between six and fifteen times higher.
This article walks through the arithmetic. The reported base from FBI IC3. The surveys and insurance-claim data that contradict it. Six structural reasons companies rationally do not report. The underreporting multipliers that the FBI and the US Department of Justice have themselves published. And four decisions downstream of the $2.77B number that are currently miscalibrated because the floor keeps getting mistaken for the figure.
1. The reported number
FBI IC3 recorded $2.77 billion in Business Email Compromise losses in 2024, across 21,442 filed complaints 1. Cumulative BEC losses reported to IC3 over the three years 2022–2024 reach $8.5 billion 2. Across the full decade since BEC became a tracked category in the IC3 taxonomy in 2015, cumulative reported losses exceed $17 billion, a growth rate of roughly 1,025% since first inclusion 1. The FBI's September 2024 public service announcement put the cumulative global BEC exposure since 2013 at approximately $55.5 billion — a figure the FBI arrived at by combining directly reported data with its own estimated adjustments 3.
Within the 2024 IC3 report, BEC ranks as the seventh-most-reported crime category by complaint count. By dollar volume it ranks second, behind investment fraud. The arithmetic implies a mean reported loss of approximately $129,000 per filed BEC complaint — a high-value, narrow-base profile consistent with BEC's operational pattern: attacker targets a specific wire-transfer or invoice-payment transaction, lands one, walks.
Mean reported BEC loss per IC3 complaint, 2024
$129,000
—
Attack volume itself is still accelerating. Abnormal AI's threat data shows BEC attack volume rising 37% between May 2024 and June 2025, with Q1 2025 alone up 30% over the prior quarter 4. The reported base is not stable; it is climbing. Whatever multiplier gets applied to translate reported to actual also scales forward from an already-rising floor.
2. The surveys that contradict it
If $2.77 billion across 21,442 complaints were the full scale of BEC exposure, the organisational surveys that sample the same population would broadly agree with it. They broadly do not.
The Association for Financial Professionals publishes an annual Payments Fraud and Control Survey, sampling several hundred US organisations across industries. The 2025 edition found that 79% of organisations were victims of payments fraud attempts in 2024 — effectively unchanged from 80% the prior year. Of those organisations, 63% cited Business Email Compromise as the number-one fraud avenue they encountered 5. Wire transfers reclaimed the top spot as the payment method most frequently targeted by BEC, reported by 63% of respondents, up from 39% the previous year 5.
Recovery rates collapsed in the same period. Only 22% of fraud-victim organisations recovered 75% or more of lost funds in 2024, down from 41% in 2023 5. Fraud was more prevalent, more successful, and less recoverable.
A second data flow, from Abnormal AI's inbox-telemetry research, puts the vendor-targeted subset — vendor email compromise, where the attacker compromises a legitimate supplier's account rather than impersonating an executive — at 83% of organisations experiencing at least one VEC attempt in 2024 4. Invoice payment fraud specifically rose 137.5% between 2023 and 2024 4.
A third data flow, from cyber insurance, points the same way. Coalition's 2024 Cyber Claims Report finds that Business Email Compromise and funds-transfer fraud combined accounted for 60% of all cyber insurance claims paid in 2024. Fifty-two percent of FTF claims originated from a BEC event, so the effective BEC footprint of cyber claim activity approaches half of all cyber claim volume. Average BEC claim severity rose 23% year over year to $35,000; FTF average claim severity sat at $185,000; overall cyber average at $115,000 6.
The arithmetic of the gap is stark. The United States has approximately six million active employer businesses 7. If the AFP survey's 79% payments-fraud incidence and 63% BEC-as-top-avenue ratios approximate the real distribution, roughly half of all US employer firms — on the order of three million organisations — encountered a BEC attempt in 2024. Against 21,442 IC3 filings. The ratio between organisations-affected and formally-reported is three orders of magnitude.
A more conservative arithmetic: count only successful losses that hit cyber insurance. Coalition alone is one of several carriers in a market covering a fraction of US businesses. The claims share that BEC and FTF jointly comprise implies that the universe of paid-out BEC incidents among insured US firms alone runs to hundreds of thousands of events annually.
Twenty-one thousand four hundred forty-two IC3 filings sit inside a universe several orders of magnitude larger.
3. Why nobody reports
Underreporting of BEC is not a victim-awareness problem. It is a structurally rational choice that repeats across nearly every category of organisation affected. Six reasons combine to produce the pattern.
Recovery yield is close to zero. AFP 2025 records the drop in recovery to 22% of victims retrieving 75% or more of lost funds 5; earlier FBI IC3 public service announcements cited recovery rates around 4% for wire-fraud incidents once the funds leave the originating bank 8. Filing an IC3 complaint costs the CFO or controller an hour of work and, statistically, returns approximately nothing of the stolen money.
Reputational and disclosure exposure is real and asymmetrical. Publicly traded US companies operate under SEC cybersecurity disclosure rules that tightened in July 2023, requiring material cyber incidents to be disclosed via Form 8-K within four business days of determining materiality 9. A BEC loss crosses the materiality threshold in many internal frameworks at loss amounts below the insurance-claim average. Triggering the disclosure chain exposes the organisation to shareholder litigation, short-position exploitation, and analyst questions — all for a $35,000 average loss.
Insurance settles without a police report. Cyber insurance policies covering BEC and funds-transfer fraud routinely pay claims without requiring law-enforcement filing as a condition. From the victim's perspective, a single insurance call yields partial recovery in weeks; a federal law-enforcement filing delivers information sharing to IC3 in hours with no recovery. The economics favour insurance exclusively.
Cross-border jurisdictional geometry does the rest. BEC fraud proceeds typically move through three to five bank accounts across two to four jurisdictions within hours of the initial transfer. Law-enforcement recovery beyond the first correspondent-bank hop requires Mutual Legal Assistance Treaty processes that average six to twelve months. Any organisation that has been through one of these does not file the next one.
Coalition's $35,000 average BEC insurance loss sits below the materiality threshold at most mid-market organisations 6. That is the band in which the controller writes off the loss, files the insurance claim, updates the vendor-master bank-account-change control, and moves on. The incident does not reach the CFO, let alone the board, let alone external law enforcement.
Finally, outside specific regulated contexts — banks under BSA suspicious-activity requirements, critical-infrastructure operators under CIRCIA, EU entities under NIS2 when fraud cascades into a security incident — corporate BEC victims have no affirmative legal duty to report to law enforcement. The default is silent.
4. The multiplier estimates
The base and the reasons are established. What remains is the multiplier. And here, for once, the US federal government has published its own number.
The director of the FBI's Internet Crime Complaint Center has stated publicly that reported cybercrime complaints represent approximately 10 to 12 percent of actual cybercrime volume 10. That is an eight-to-ten-times multiplier, officially sourced. Separate FBI public statements put the reporting rate at approximately 15% of online crime 11, implying a roughly 6.6x multiplier. The US Department of Justice has estimated that roughly one in seven cybercrimes is reported 12, implying a 7x multiplier. These three estimates bracket the same range: for cybercrime specifically, actual volume runs somewhere between six and ten times the reported base.
The ACFE's 2024 Report to the Nations analysed 1,921 confirmed occupational fraud cases across 138 countries, with losses in the analysed cases exceeding $3.1 billion 13. The ACFE report does not publish a named multiplier for BEC underreporting specifically. The "10–15x" figure widely cited in fraud-industry commentary is a compound of FBI, DOJ, ACFE, and insurance-industry inputs, not a single primary statement. It is useful as a directional consensus of practitioners; it is not as authoritatively sourced as the FBI IC3 director's 10–12% statement.
Applied to the 2024 IC3 base, the range is:
- DOJ one in seven (7x): $19 billion
- FBI IC3 director 8–10x: $22–28 billion
- Industry consensus 10–15x: $28–42 billion
The midpoint of the FBI/DOJ-backed range sits near $25–30 billion annual US BEC losses — an order of magnitude above the $2.77 billion the FBI publishes itself. That is the article's headline finding.
5. Why the gap matters
Four decisions downstream of the $2.77 billion number are currently miscalibrated because the number is being used as a measurement rather than a floor.
Corporate security budget allocation calibrates against industry-reported loss averages. A per-capita BEC exposure calibrated on $2.77B / 21,442 = $129K per filed complaint sets one budget level; a real per-incident exposure several times that, for the organisations actually affected, sets a different one. The downstream effect shows up in fraud-prevention headcount, payment-verification software procurement, and vendor-master-file hygiene investment.
Cyber insurance pricing draws on both IC3 public data and insurers' own claim files. When the public data understates claim activity by an order of magnitude, the delta between actual and priced risk accrues to carrier P&L, exposes carriers to adverse selection, or produces jagged year-over-year severity revisions — Coalition's observation that BEC severity rose 23% in 2024 is closer to the operational truth than IC3's quieter year-over-year growth 6.
Legislative and law-enforcement resource allocation calibrates in part against IC3 reported totals. If actual US BEC losses run $25–40 billion against $2.77 billion reported, the implied federal enforcement resource requirement is roughly ten times what current IC3 reporting justifies. Oversight committees fund what the official number tells them to fund.
Enterprise vendor and counterparty-verification spend — the budgets that flow toward KYB platforms, supplier-data tools, payment-verification services, bank-account verification, and cross-border business registry access — depends on whether the CFO sees B2B fraud as a $2.77 billion industry-wide annoyance or a $30 billion strategic exposure. Same data point, different multiplier, different budget decision.
Closing
The $2.77 billion number will be cited again this year in congressional hearings, insurance underwriting decks, and security-vendor marketing. Every citation will treat it as a measurement.
It is not a measurement. It is what the FBI's own IC3 director has publicly acknowledged is approximately 10 to 12 percent of the real number. Reasonable people applying FBI and DOJ multipliers reach a 2024 US BEC exposure estimate in the $19 to 28 billion range. Reasonable people using more aggressive fraud-industry multipliers reach higher, into the $28–42 billion range. No reasonable person working from the evidence lands at $2.77 billion as the true number.
The cost of treating a floor as a figure compounds. Corporate budgets get built on it. Laws get passed on it. Enterprise vendor spend gets approved on it. Until the underreporting ratio itself becomes part of the default citation — until "$2.77 billion reported" gets replaced with "$2.77 billion reported, approximately 10% of actual" — the fraud economy operates at one scale and the public conversation operates at roughly one-tenth of that scale.
That gap is the story.
Footnotes
-
FBI Internet Crime Complaint Center, "2024 IC3 Annual Report," April 2025. Verified 2026-04-17 at ic3.gov/AnnualReport/Reports/2024_IC3Report.pdf. ↩ ↩2 ↩3
-
Nacha, "FBI's IC3 Finds Almost $8.5 Billion Lost to Business Email Compromise in Last Three Years," 2025. Verified 2026-04-17 at nacha.org/news/fbis-ic3-finds-almost-85-billion-lost-business-email-compromise-last-three-years. ↩
-
FBI Internet Crime Complaint Center, "Business Email Compromise: The $55 Billion Scam," PSA dated 11 September 2024. Verified 2026-04-17 at ic3.gov/PSA/2024/PSA240911. ↩
-
Abnormal AI, "Threat Report: BEC & VEC Attacks Show No Signs of Slowing," 2024. Publisher: abnormal.ai. Verified 2026-04-17. ↩ ↩2 ↩3
-
Association for Financial Professionals, "2025 AFP Payments Fraud and Control Survey Report," April 2025. Survey of approximately 500 US organisations. Verified 2026-04-17 at financialprofessionals.org/training-resources/resources/survey-research-economic-data/details/payments-fraud. ↩ ↩2 ↩3 ↩4
-
Coalition, "2024 Cyber Claims Report," 2025. Publisher: coalitioninc.com. Verified 2026-04-17. ↩ ↩2 ↩3
-
US Census Bureau, Business Dynamics Statistics, and US Small Business Administration Office of Advocacy, "Frequently Asked Questions About Small Business," 2024. Approximately 6 million active employer businesses, approximately 33 million total small businesses when including non-employer firms. Verified 2026-04-17 at advocacy.sba.gov. ↩
-
FBI Internet Crime Complaint Center, "Business Email Compromise: The $50 Billion Scam," PSA dated 9 June 2023. Historical recovery-rate context. Verified 2026-04-17 at ic3.gov/PSA/2023/psa230609. ↩
-
US Securities and Exchange Commission, "Final Rule: Cybersecurity Risk Management, Strategy, Governance, and Incident Disclosure," 33-11216, effective September 2023. Verified 2026-04-17 at sec.gov/rules/final/2023/33-11216. ↩
-
Statement attributed to the director of the FBI Internet Crime Complaint Center on public-reporting rates for cybercrime; see Slate, "The Real Reasons Why Cybercrimes Are Vastly Underreported," February 2018, and subsequent coverage. Verified 2026-04-17 at slate.com/technology/2018/02/the-real-reasons-why-cybercrimes-are-vastly-underreported.html. ↩
-
FBI public statements on cybercrime reporting rates, as summarised by CSO Online and other outlets. See CSO Online, "Why Businesses Don't Report Cybercrimes to Law Enforcement." Verified 2026-04-17 at csoonline.com/article/567307/why-businesses-don-t-report-cybercrimes-to-law-enforcement.html. ↩
-
US Department of Justice estimate that approximately one in seven cybercrimes is reported. See Third Way, "The Need for Better Metrics on Cybercrime." Verified 2026-04-17 at thirdway.org/memo/the-need-for-better-metrics-on-cybercrime. ↩
-
Association of Certified Fraud Examiners, "Occupational Fraud 2024: A Report to the Nations," 2024. Verified 2026-04-17 at acfe.com/-/media/files/acfe/pdfs/rttn/2024/2024-report-to-the-nations.pdf. ↩
About the Author
Sebastian Zerniak
CEO and Founder, B2Trust
Sebastian Zerniak is the founder and CEO of B2Trust. He writes about business identity, verification, and the trust mechanics underneath B2B commerce.
LinkedIn →